A new wave of cybercrime that preys on lax hiring and internal security processes requires HR departments to be more vigilant, according to two attorneys who spoke to HR Dive.
The attacks are often perpetrated by state actors — most prominently backed by North Korea, though other nations also may be implicated — and involve the use of fake job candidates to obtain remote work positions at U.S. companies, said Matthew Welling, partner, and Neda Shaheen, associate, both of Holland & Knight. Once hired, these individuals may funnel income received from affected employers to their host countries.
Federal law enforcement officials uncovered one such scheme in 2024, alleging that a U.S. national conspired with North Korean information technology workers to generate $6.8 million in funds from Fortune 500 companies over a period of about three years. Last month, the U.S. Department of Justice announced that two other U.S. nationals had been sentenced to prison for their role in a North Korean remote work fraud scheme, Cybersecurity Dive reported.
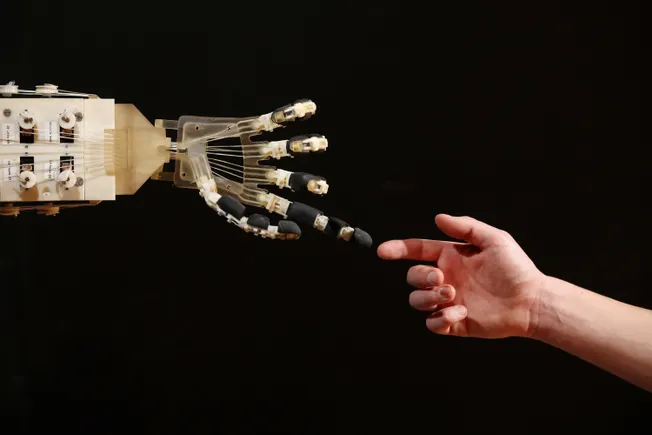
Perpetrators employ several different methods to infiltrate employers, including deepfakes — a category of digitally-produced, fabricated content that attempts to pass for real job candidates. It takes bad actors a short amount of time to create deepfaked job candidates that are capable of duping employers during the hiring process.
“They don’t always follow a common pattern, but there are some general commonalities,” said Welling, who noted that victims of the schemes frequently uncover multiple fake employees. “What we’ve seen from organizations that know what they’re looking for is that often, if they find one of these actors, they find more.”
How HR teams spot suspicious activity
Identifying fraudulent employees requires interdepartmental coordination and knowledge of potential red flags, Welling said.
For instance, the actor may connect to an unexpected place within the organization’s systems, including those for which they do not or should not have access. Another example involves the use of unauthorized virtual private network services. Outside security vendors can help alert employers to such activity.
In the recruiting process, Welling said employers should be wary of situations in which an employee’s qualifications do not match what they’ve provided in their written material, or where the employee’s voice or appearance changes.
Finally, employers may receive notifications from law enforcement that an employee is fraudulent. These notifications tend to be retroactive in nature given the length of the typical criminal investigation, Welling noted, and regulators often don’t want to tip off offenders by notifying employers.
If a fraudster as identified by law enforcement has accessed a heavily regulated database or platform, federal and state privacy laws may require employers to disclose that an electronic breach has occurred, he added.
Employers also may face sanctions should a bad actor use funds derived from the scheme to finance unlawful activities, said Shaheen. Sanctions can be imposed on a strict liability basis, she noted, meaning that no intent on the part of the employer is required in order for a violation to occur.
“Companies could face consequences even if they unknowingly hire somebody and give them their regular salary,” Shaheen said. “The company is balancing not just being a victim of the fraud but also being subject to legal and regulatory scrutiny.”
Action items once suspected fraud is uncovered
The process for addressing a false employee follows that of a typical HR investigation, Welling said, with the most comparable scenario being insider risk operations. “These people are going to look the most like malicious insiders,” Welling said of fraudulent employees.
It’s not always the case that HR opens its investigation suspecting criminal conduct, he added, but employers that have a high degree of confidence that a bad actor is present may decide to preemptively restrict systems access to those individuals out of an abundance of caution.
Not every red flag is the sign that an employee is actually a criminal. Welling said employees may have legitimate explanations for suspicious activity. For instance, an employee may be logging onto their computer in an unusual location because they are caring for a family member with a prolonged illness. Ideally, the employee can communicate this information ahead of time, but such examples do show the challenges of recognizing fraud, he added.
Additionally, bad actors behind worker fraud schemes often are very cooperative and communicative with employers who suspect them of wrongdoing, Welling noted. Clients have seen suspected fraudsters go as far as to return their company laptops or arrange for an in-person contact to meet the employer at an office to assuage concerns, one of several “extreme steps” that may be taken just to ensure the scheme can persist a while longer.
“The actors seem to be motivated to get one more paycheck or a severance payment or something like that,” Welling said. “For an organization that doesn’t know what they’re looking at yet, it doesn’t raise the same alarm as someone who behaves like a criminal.”
If one bad actor is successful in getting hired at a firm, they can act as a reference for other such actors using their knowledge of the employer’s hiring process, Welling added.
Internally, HR should work with legal and finance teams so that patterns of criminal activity can be identified and followed up on, Welling said. If fraud is uncovered, HR also can relay observed patterns of suspicious behavior to managers and other leaders for future reference.
Fake worker schemes tend to affect large remote workforces and roles within organizations that don’t require minute-to-minute interaction with other employees, Welling said. Such roles also tend to be amenable to the use of artificial intelligence tools that would help the fraudster fulfill the work.
Employers should take care to document any actions taken to address suspected fraud as well as all work done to substantiate their suspicions, Welling continued. This ensures the company can protect itself from any future legal claims and can point to the fact that it followed policies and procedures that were both reasonably developed and involved the correct members of the organization.
“These are all decisions that companies are going to have to make, but they should at least have a playbook,” he said.




Leave a Reply